Doot – Top Data Protection Platform
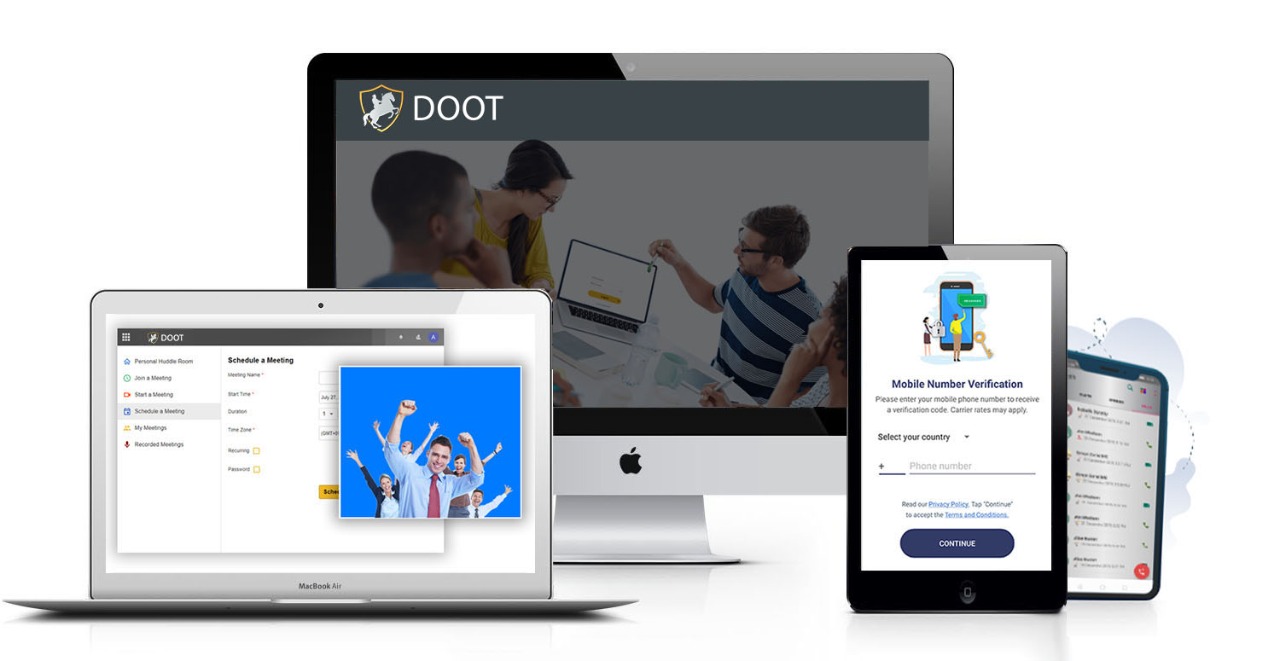
Doot, a next-level security enhancement protocol-based application uses device-to-device encryption which is superior to traditional end-to-end encryption and is feature-rich with a user experience that surpasses many similar apps. Doot, the top data protection platform also complies with country-specific privacy requirements. In addition, the leading data security service, Doot also provides the same integrated security protocols for its organizational suite application, allowing businesses of all types to run their operations securely from anywhere, and anytime.
Solutions
A full cloud-based external and internal collaboration suite
1
2
3
4
5
6
7
1
Doot Connect
2
Doot Office
3
Doot Mobile Messaging
4
Doot Learning
5
Doot Social
6
Doot Collaborate
7